

With Corvina Cloud App software it is possible to access Corvina Cloud infrastructure to get access to devices via VPN connection. Proper credentials are required to access Corvina Cloud, given by a local reseller or by the organization owner.
Following requirements needs to be satisfied to follow this guide:
1. Corvina Cloud App software (Download here)
2. Superuser account to use with Corvina Cloud App (Ask to your local reseller )
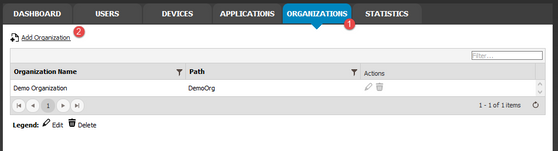
Manage Organizations
From [ORGANIZATIONS] tab click on Add Organization
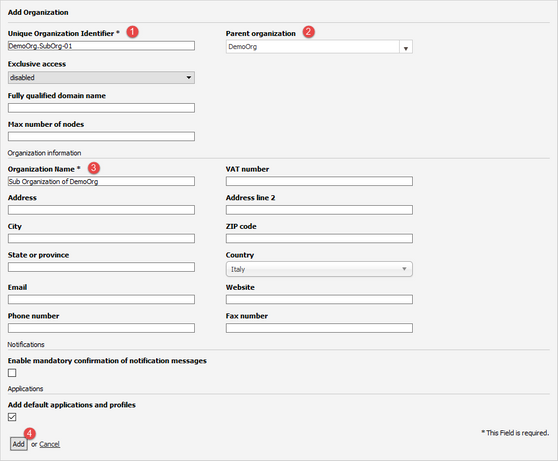
In the following window insert:
1. Unique Organization Identifier: this is the identifier between sub organizations and it must be unique
2. Parent Organization: choose the root organization or a sub organization as parent (if left blank, the root organization will be selected)
3. Organization name: this is the name of organization displayed in Organizations list
Fill the other fields by inserting the organization common details (phone number, address, position, website etc...) and then click on [Add] button to create the organization.
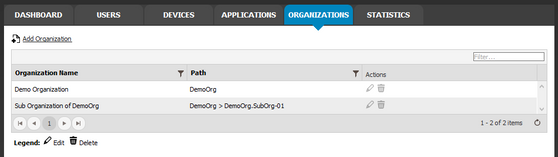
The added organization will be displayed inside the organization list.
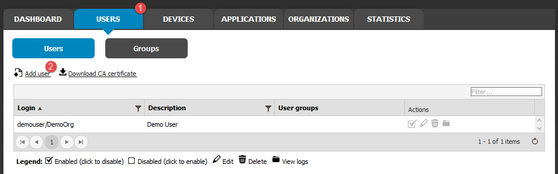
Manage Users
To create a new user, from [USERS] tab click on Add user
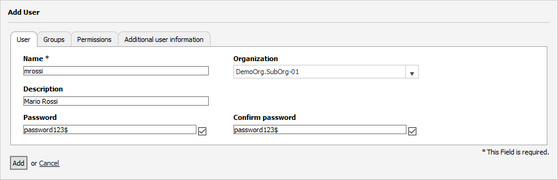
From User tab, set the following fields:
1. Name: this the user name, it must be unique in users, gateways and endpoints
2. Organization: this is the organization to which the user will be long to (if left blank, the root organization will be selected)
3. Password: must be at least 8 character and contain at least one non-alphanumeric character
4. Optionally, a Description can be added to make searches easier
Click on Add button to add the user.
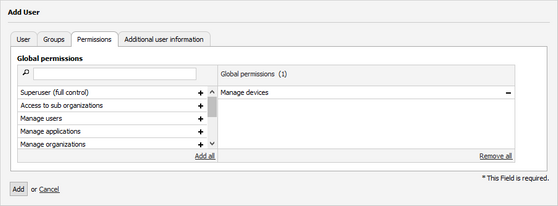
Permissions
In this tab can be selected the permissions a user has on the other nodes and users of the Corvina Cloud. Items on the right column of the multiselect box are the permissions granted to the user, while those in the left column can not be used by the user. Click on the + on the right-hand side of the item to grant a permission, on - to remove the permission.
The user can be granted several permissions:
1. Superuser (full control): The user can fully manage the Corvina Cloud
2. Access to sub organizations: The user can access organizations
3. Manage users The user can manage other users
4. Manage devices The user can manage devices
5. Manage applications: The user can manage the actions
6. Manage organizations: The user can manage the organizations
7. Use the API: The user can access and use the Corvina Cloud’s API. (Feature not yet supported)
8. Direct access to application: The user can only connect to a predefined device through a predefined application (see Direct Access for additional details)9. Push route to GREEN | BLUE |
9. ORANGE zone: When one or more of these options is selected, appropriate routes to the sub-nets governed by the Corvina Cloud will be pushed to the user. (Feature not yet supported)
Any combination of these values can be associated to the user.
Application Policies
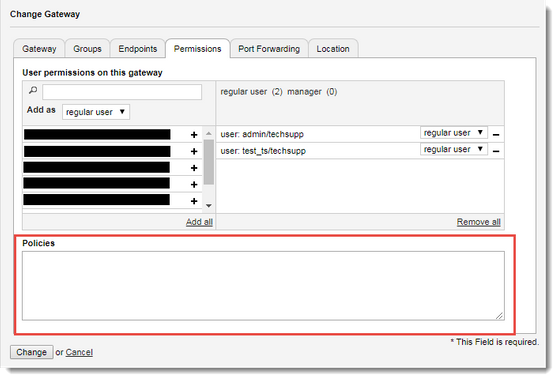
Policies allows to manage access to individual gateway / endpoint applications in order to allow or block one user or any. To do this, user needs to access Corvina Cloud with "manage device" permission.
Go in Device tab and edit the Gateway by clicking on the pencil icon. Navigate to Permissions tab and set the user to allow to use the endpoint application as "regular user" or "manager" of Gateway. Access policies can be specified in the text box called Policies, as shown in picture below.
The policies rules are text strings with following syntax:
ALLOW/DENY ‘Application/Organization’ ON EndpointName TO UserName
Wildcard * is accepted in any position and will indicate any (application, endpoint, user).
Order of rules will determinate priority: the first rule matched will be the one to be applied.
If no rule is matched, default rule will be ALLOW *, which means: “everything will be accepted”.
In case it is needed to have full control on the application access for each endpoint the best practice is setting the last rule as DENY: this will block all the accesses between application, endpoint, user not directly specified from policies.
Denying all application from an endpoint will also block users involved in the rule, into connecting by VPN.
Use cases examples
DENY
Everything is blocked: no user see nothing in no endpoint.
DENY 'AppName/Organization' ON Endpoint TO User
Everything visible except the application ‘AppName/Organization’ on Endpoint, for User.
ALLOW 'AppName/Organization' ON Endpoint TO User
DENY
Everything is blocked except application ‘AppName/Organization’ on Endpoint, for User.
DENY * ON Endpoint TO User
Everything is blocked on Endpoint. User is not allowed to create VPN to Endpoint.
DENY * ON * TO User
Everything blocked for User on every endpoint. User is not allowed to create VPN to any endpoint.
ALLOW 'AppName/Organization' ON Endpoint TO User1
ALLOW 'AppName/Organization' ON Endpoint TO User2
DENY
Everything blocked on any endpoint except for 'AppName/Organization' application on Endpoint. Both User1 and User2 are allowed.
SMART AUTOMATION APS ∙ BRANSAGERVEJ 5 ∙ DK-9490 PANDRUP ∙ DENMARK ∙ PHONE +45 7734 9960 ∙ SALG@SMARTDK.COM ∙ CVR: 31769574 ∙ WWW.SMARTDK.COM